Exploiting the BOSS 915 pager

Pagers are widely used in emergency services. The Swissphone BOSS 915 is one of the most common models and I found an exploit for it. It's trivial to execute and based on a very critical design flaw that allows anyone with device access to read out a non-salted, hashed password. This password allows you to read out the configuration of other pagers, programmed by the same organisation, as they often use the same password for all their pagers. This in turn allows you to modify a pager's configuration without anyone noticing.
Quick-start
Pagers are widely used in emergency services to notify firefighters, paramedics, and the like of alarms. They serve a quite critical role there. Many pager models are programmed/configured by an operator in conjunction with dispatch. This configuration is, as far as I know, not to be known by anyone. After all, you don't want anyone to just sniff around the pager network. This is why the Swissphone DE10A hardware (which is what the BOSS 915/9135 is) allows to be locked. When locked, the pager's configuration cannot be read without knowing the programming password.
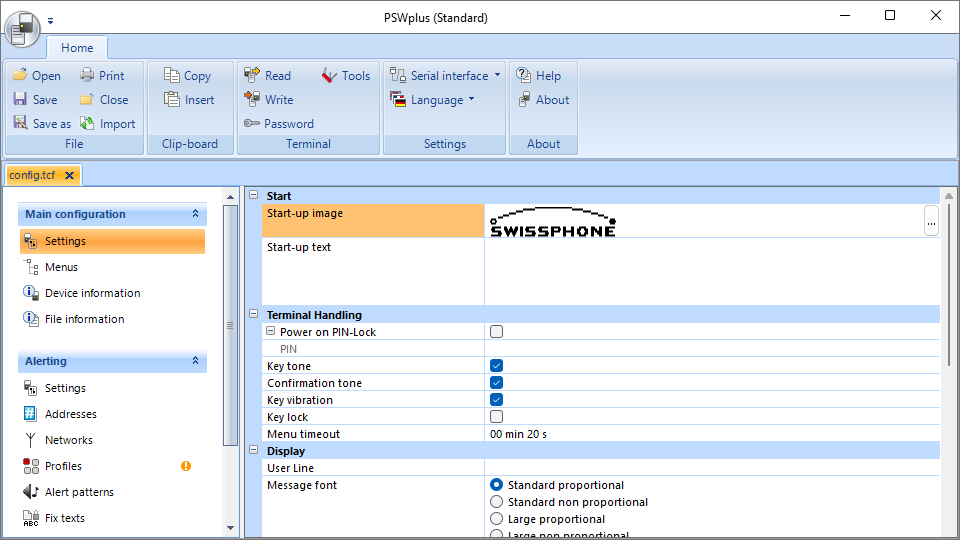
Main window of the configuration software
For configuration, Swissphone offers a Software on their website for all pagers since the DE10A line of devices. It interfaces with the pager through a custom UART based serial protocol. You can use simple USB to UART converter to connect to the pager, for which you can find plenty of information online. As you can see, it's not that hard to configure a pager yourself. That's why a secure way to lock a pager is important.
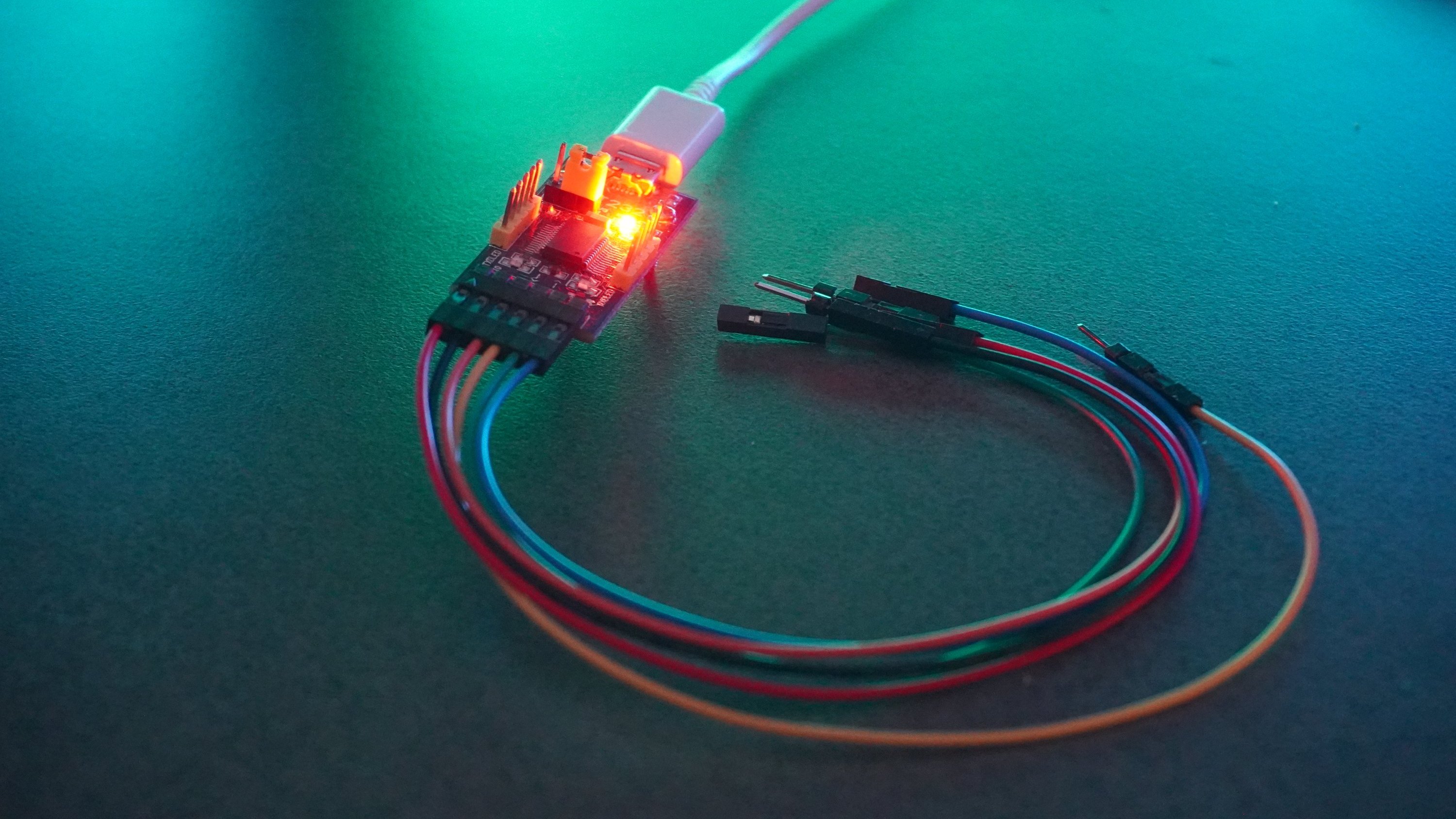
USB to UART adapter
The pager stores its configuration in logical storage blocks on an EEPROM. These storage blocks have an id, size, version, and access permissions (RWIP, not sure what I and P mean). There are many blocks for all kinds of functions. Different firmware versions have different versions of storage blocks, because of small changes in functionality across firmware versions.
Technical difficulties
There are two critical weak points with the locking mechanism that lead to an exploit.
Normally, this kind of thing would work something like this: When a programming password is set, the pager would receive the password, hash it with a salt and store that hash and the salt in a safe, inaccessible place. To unlock the pager, the software would send the password, the user entered, to the pager, which in turn would hash this password with the salt and compare the calculated hash with the stored one. If they match, the pager would unlock itself.
However, this is not quite what's happening. When a programming password is set, the software itself calculates the hash without any salt and sends it to the pager which stores it. To unlock the pager, the configuration software asks the user for the password, hashes it and sends that hash to the pager, which compares it with the stored hash and unlocks itself if they match. This means, the hash is effectively a password, as you only need it to unlock a pager, not the password. However, as the hashing function is only SHA1, it's trivial to crack the hash using a rainbow table. I think any security expert is screaming right now…
But there's more! We still need a way to obtain this password and that's the crazy part. Pagers on firmware version lower than 4 straight-up don't have a way to be locked. You might wonder, how that works then. It's quite simple. There's storage block E100 which contains the password hash among other locking related things. When you set a programming password, the software calculates the password hash and writes it to the storage block. When you connect a pager to the configuration software, the software reads this password hash, asks the user for the password and calculates a hash from the given password. If both hashes match, it continues. If not, it will increase a failed counter, which is also in this storage block and refuse to work with this pager.
This is like having a password to enter the castle which is checked by someone at every gate. Except there's one gate where you have to check the password yourself, by reading it off the wall and deciding yourself if you enter or not. At this gate you could just ignore the password and enter, or you could remember it and use it at any other gate to get in. It's ridiculous! How did this firmware go out the door at Swissphone?
The exploit itself
Now the exploit should be obvious:
- Get a locked pager with firmware version less than v4.0
- Read out the storage block E100
- You now have the hash. That's all you need!
- Optional: Crack the hash using a rainbow table.
- Profit!
This makes it a really easy social engineering exploit: Give an exploitable pager to your organisation for programming and read out the password later.
Final thoughts
As I said, this is only valid for older firmware versions, so Swissphone has to have noticed their mistake around 2016 when version 4 came out. This makes sense, as you can find rumors of a password remover tool in a forum page and a matching video that shows exactly that. However, there are still a lot of pagers around with that old firmware version, which means it's rather easy to acquire an exploitable one and pull off a simple social engineering technique. On to of that mess, it's quite expensive to do a firmware upgrade, so many not-so-well funded organisations will probably never invest in firmware updates, sticking with the version, the devices came with and allowing their users to read them out.
At first, I was unsure whether to publish this article, but I'm at a point where it's clear that there are many such structural problems in a lot of companies and organisations that do infrastructure for emergency services. And if there's one thing we can't have, it's this infrastructure not working! So by publishing this article, I'd like to show people that even a stupidly expensive and certified device can have issues, a 22-year-old student can find in their free time and exploit.
More from the pagerverse
To uncover this exploit, I did a lot of digging around the entire ecosystem. A lot of it went nowhere, but is very interesting nonetheless. So I encourage you to read my other articles on the DE10A pager hardware and its surrounding ecosystem if you enjoyed this one.
- The DE10A pager
- 📌 The BOSS pager exploit
- 🔜 A cool startup image for the BOSS pager
- 🔜 The Swion Terminal Dump